Read the Full Report
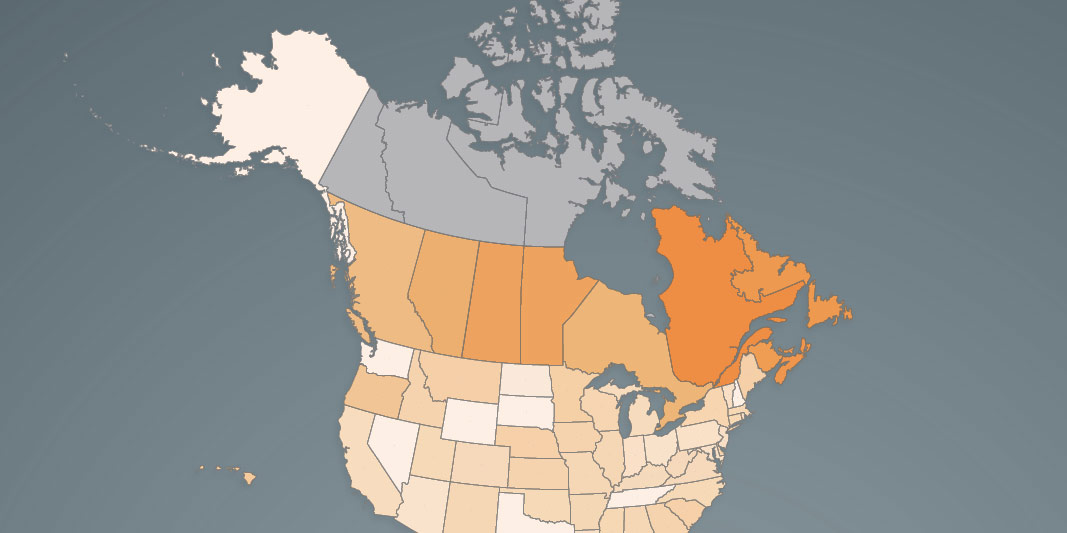
Read the Full Report View the Infographic - Income Tax Rate at CA$50,000
View the Infographic - Income Tax Rate at CA$50,000 View the Infographic - Income Tax Rate at CA$50,000 (Atlantic Canada)
View the Infographic - Income Tax Rate at CA$50,000 (Atlantic Canada) View the Infographic - Income Tax Rate at CA$75,000
View the Infographic - Income Tax Rate at CA$75,000 View the Infographic - Income Tax Rate at CA$75,000 (Atlantic Canada)
View the Infographic - Income Tax Rate at CA$75,000 (Atlantic Canada) View the Infographic - Income Tax Rate at CA$150,000
View the Infographic - Income Tax Rate at CA$150,000 View the Infographic - Income Tax Rate at CA$300,000
View the Infographic - Income Tax Rate at CA$300,000 Read the News Release - Canada
Read the News Release - Canada Read the News Release - Atlantic Canada
Read the News Release - Atlantic Canada
 Read the Essay - Canada's Carbon Tax Plan is Beyond Policy Redemption
Read the Essay - Canada's Carbon Tax Plan is Beyond Policy Redemption Notes and References - Canada's Carbon Tax Plan is Beyond Policy Redemption
Notes and References - Canada's Carbon Tax Plan is Beyond Policy Redemption Read the Essay - Reforming the Federal Government's Carbon Tax Plan
Read the Essay - Reforming the Federal Government's Carbon Tax Plan Notes and References - Reforming the Federal Government's Carbon Tax Plan
Notes and References - Reforming the Federal Government's Carbon Tax Plan Read the News Release
Read the News Release